The ASEC analysis team monitors phishing email threats with the ASEC automatic sample analysis system (RAPIT) and honeypot. This post will cover the cases of distribution of phishing emails during the week from December 18th, 2022 to December 24th, 2022 and provide statistical information on each type. Generally, phishing is cited as an attack that leaks users’ login account credentials by disguising as or impersonating an institute, company, or individual through social engineering methods. On a broader note, the act is a technical subterfuge that enables the threat actor to perform attacks such as information leaks, malware distribution, and fraud against various targets. The focus of this post will be on the fact that phishing attacks mainly occur through emails. We will also provide a detailed classification of various attack methods that are based on phishing emails. Furthermore, we will make an effort to minimize user damage by introducing new attack types that have never been found before and emails that require users’ caution, along with their keywords. The phishing emails covered in this post will only be those that have attachments. Emails that have malicious links in the body without attachments will be excluded.
Phishing Emails
During this week, the most prevalent threat type seen in phishing email attachments was Infostealer, taking up 35%. Infostealer includes malware such as AgentTesla and FormBook, and they leak user credentials saved in web browsers, emails, and FTP clients.
It was then followed by FakePage, which took up 34%. FakePages are web pages where the threat actor has imitated the screen layout, logo, and font of the real login pages or advertising pages, leading users to enter their account and password information. The input information is sent to the threat actor’s C2 server or used to induce users to access other fake websites. See <FakePage C2> below
The third-in-line was Worm Malware with 11%. Worm is a type of malware that has a feature to spread, where it uses various methods for spreading, with one of them being using the SMTP protocol to send emails in mass quantity.
Aside from these, Downloader (10%), Trojan (6%), and Dropper (4%) types were detected.
The threat types using phishing email attachments and their order of prevalence are similar to the order of malware distribution published weekly in the <ASEC Weekly Malware Statistics>.
File Extensions in Phishing Emails
We have identified which file extensions were used by the threats above for the distribution of email attachments. FakePages were distributed with PDF documents or web pages scripts (HTML, HTM) that must be executed with a web browser. Other malware, including Infostealer and downloader, came attached to emails with various file extensions including compressed files (RAR, GZ, TAR, Z, etc.), IMG disk image files, and DOCX document files. With the exception of FakePages that are distributed through web pages script files and PDFs, other malware types were distributed with a variety of file extensions regardless of the threat type. Among the phishing email attachment types, the compressed file variant showed a particularly showed a high percentage with 29%.

Cases of Distribution
The following are distribution cases that occurred during the week from December 18th, 2022 to December 24th, 2022. The cases will be classified into fake login pages and malware types, including Infostealer, Downloader, Exploit, and Backdoor. The numbers in email subjects and attachment filenames are unique IDs and may vary depending on the email recipient. Distribution cases with Korean subjects were also found. These are cases that specifically targeted Korean users instead of propagating themselves globally using the identical English subject and text.
Case: FakePage
| Email Subject | Attachment |
| FW: RE: FW: FW: B/L Notice – SWA0259760 | AWB-87466784.html |
| Incoming Call For ****@****.com -: Caller ID Received | Ref# Voice 230 (455763).html |
| Incoming Mail Error | 6_Suspended_Messages-01.html |
| sin asunto (283304) | Factura_F_2690_F548FD90-ECC4-41FA-8F60-8ECDB27DFA07.html |
| TT USD $20,080.49 | SWIFT.html |
| USD Payment COPY | USD-INVOICES.shtml |
| WIRE USD $33,242.31 | SWIFT.html |
| Ahoj | Harrison Family Foundation Newsletter.pdf |
| Atencion! ultima advertencia (160568) | CFEG380213QM5_Factura_B_43609_BA8FE438-D923-4772-BA1-166ED8359417.pdf |
| Aviso de Factura – REF (129397) | CFEG380213QM5_Factura_B_43609_BA8FE438-D923.pdf |
| Buenas Noches, para para solicitarle la factura S58023046299758 – adjunto Detalles (233574) | Archivos-F2654.pdf |
| Comprobante Fiscal Digital No. – (984647) | 01_365896d-a55z-7lkj-lamshd-36598e32mb0101.pdf |
| FW: [SP-22-288938] **** **** Sales Portal : Regarding your Spiff claim | Document_19_dec_81054642.pdf |
| LAS FACTURAS PARA TRAMITE DE PAGO (773046) | FACTURA ST146_VANGUARDIA ENERGIA_1988532.pdf |
| POR FAVOR CONFIRMAR Y CORREO. REALIZO EL PAGO DE LA COTIZACIËN T597517902 (422191) | Fichero-H1332.pdf |
| RV: Saludos, envio facturas 15 Diciembre 2022 – REF – (941489) | factura.pdf |
Case: Malware (Infostealer, Downloader, etc.)
| Email Subject | Attachment |
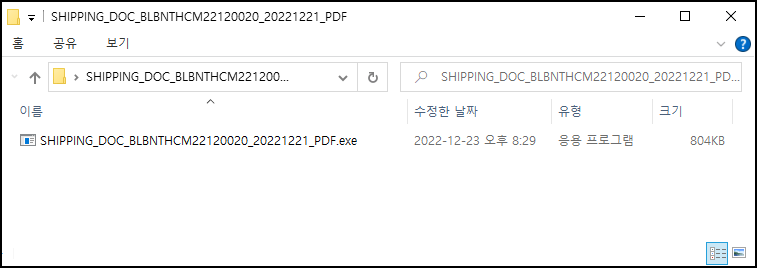
| RE: Shipping PI CS/2022-23/024 Documents & Shipment advise Est. E.T.D 28 DEC | SHIPPING_DOC_BLBNTHCM22120020_20221221_PDF.rar |
| Payment copy | payment copy.gz |
| PO#3006376 Chile Orders | PO#3006376 Chile Orders.PDF.Z |
| Fwd: Zaplata | Zaplata.jpeg.img |
| nice pics | coolphotos.pif |
| Re[2]: very nice pics | greatpic.gif.exe |
| wonderful pics | superact.gif.exe |
| ORDER ENQUIRY | ORDER ENQIRY #093727664.rar |
| DHL Shipment Notification | dhl dd.rar |
| Payment copy | payment copy.gz |
| Buchung für neues Jahr | Dokumentieren.docx |
| Re[5]: cool pics | great_imgs.gif.exe |
| New Inquiry/22-0567 | Euro industriel New Inquiry 221219.tar |
| Re[4]: very wonderful pics only for you | great__photos.exe |
| INV. & PL FOR COMERCIAL ECCSA S.A. SEA SHIPMENT | Payment Invoice.rar |
| Sistema New Order – 221221-2009 | Sistema-221221-2009.img |
| T.HALK BANKASI A.S. 22.12.2022 Hesap Ekstresi | Halkbank_Ekstre_20221222_073809_405251-PDF.tar |
| Due Invoice Payments | Nvoices status.rar |
| beautiful pics | thephotos.pif |
| Re: Payment (URGENT BANK ACCOUNT) | INVOICE_VM220200200305.IMG |
| Re:Payment Advice | INWARDREMITANCE48990021337565990_pdf.img |
| Re:Transfer Confirmation | Payment Confirmation 789001_pdf.img |
| order | ORDER 19-12-22.IMG |
| ASUNTO: Asesoramiento de Standard Chartered Bank | Pago_Aviso.img |
| Re: Payment (URGENT BANK ACCOUNT) | INVOICE_VM220200200204.IMG |
Keywords to Beware of: ‘RAR Compressed File

FakePage C2 URL
When users enter their IDs and passwords on the login pages among the FakePages created by the threat actor, their information is sent to the attacker’s server. The list below shows the threat actor’s C2 addresses of fake login pages distributed during the week.
- hxxps://gojobs.in/xzx/dhl.php
- hxxps://formspree.io/f/mayzwypz
- hxxps://formspree.io/f/xvonpqea
Preventing Phishing Email Attacks
Attacks using phishing emails are disguised with content that can easily deceive users, such as invoices and tax payments, to induce users to access fake login pages or execute malware. Fake login pages are evolving by the second to closely resemble the original pages. The attackers pack malware in compressed file formats to escape the attachment scans of users’ security products. Users must practice strict caution and refer to recent cases of distribution to avoid being exposed to infection by malicious phishing emails. The ASEC analysis team recommends users follow the email security guidelines below.
- Do not execute links and attachments in emails from unverified senders until they are proven to be credible.
- Do not enter sensitive information such as login account credentials until the site is found to be reliable.
- Do not execute attachments with unfamiliar file extensions until they are found to be reliable.
- Use security products such as antimalware software.
According to the MITRE ATT&CK framework, phishing email attacks correspond to the following techniques.
- Phishing for Information (Reconnaissance, ID: T1598[1])
- Phishing (Initial Access, ID: TI1566[2])
- Internal Spearphishing (Lateral Movement, ID: T1534[3])
Subscribe to AhnLab’s next-generation threat intelligence platform ‘AhnLab TIP’ to check related IOC and detailed analysis information.
Source: https://asec.ahnlab.com/en/45237/
