HijackLoader is a modular malware loader discovered in 2023, capable of delivering payloads and employing various evasion techniques. Recently uncovered modules feature advanced tactics such as call stack spoofing, virtual machine detection, and persistence through scheduled tasks. Affected: malware, cybersecurity sector, antivirus software
Keypoints :
- HijackLoader is a malware downloader first identified in 2023, continually receiving updates.
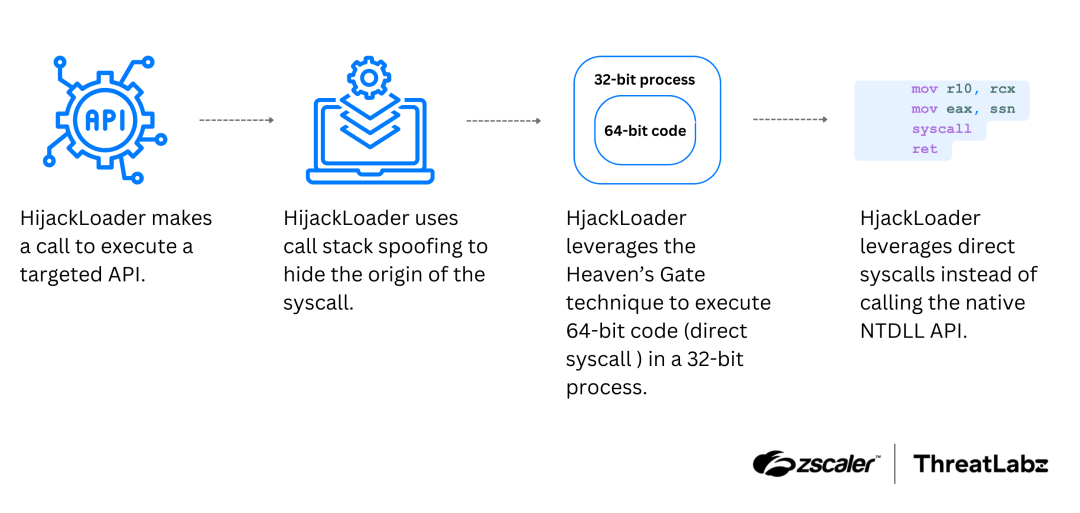
- New modules implement call stack spoofing to obscure the origin of function calls.
- Anti-VM checks are introduced to prevent execution in analysis environments.
- The malware can establish persistence through scheduled tasks.
- Recent updates include various evasion tactics enhancing its anti-detection capabilities.
MITRE Techniques :
- T1574.002 – Hijack Execution Flow: DLL Side-Loading: Uses DLL sideloading for execution.
- T1027.007 – Dynamic API Resolution: Utilizes SDBM and CRC32 for API resolution.
- T1027.003 – Steganography: Hides modules in a PNG image using steganography.
- T1140 – Deobfuscate/Decode Files or Information: Uses XOR for module decoding.
- T1057 – Process Discovery: Checks running processes against antivirus names.
- T1620 – Reflective Code Loading: Reflectively loads modules using legitimate DLLs.
- T1547.001 – Registry Run Keys / Startup Folder: Creates shortcuts in Windows Startup for persistence.
- T1197 – BITS Jobs: Employs BITS Jobs for persistent execution.
- T1053 – Scheduled Task/Job: Uses the modTask module to create scheduled tasks.
- T1548.001 – Abuse Elevation Control Mechanism: Utilizes UAC bypass mechanisms.
- T1055 – Process Injection: Conducts process injection to deploy its final payload.
- T1497 – Virtualization/Sandbox Evasion: Implements multiple evasion techniques against virtual environments.
- T1562.001 – Impair Defenses: Uses PowerShell commands for Windows Defender exclusion.
Indicator of Compromise :
- SHA256 67173036149718a3a06847d20d0f30616e5b9d6796e050dc520259a15588ddc8 HijackLoader sample
- SHA256 7b399ccced1048d15198aeb67d6bcc49ebd88c7ac484811a7000b9e79a5aac90 HijackLoader sample
- SHA256 6cfbffa4e0327969aeb955921333f5a635a9b2103e05989b80bb690f376e4404 HijackLoader sample
- SHA256 b2b5c6a6a3e050dfe2aa13db6f9b02ce578dd224926f270ea0a433195ac1ba26 HijackLoader sample
- SHA256 d75d545269b0393bed9fd28340ff42cc51d5a1bd7d5d43694dac28f6ca61df03 HijackLoader sample
Full Story: https://www.zscaler.com/blogs/security-research/analyzing-new-hijackloader-evasion-tactics