Trend Research reveals the exploits of Water Gamayun, a suspected Russian threat actor leveraging a zero-day vulnerability (CVE-2025-26633) in Microsoft Management Console to deploy malware. Their methods include custom payloads, data exfiltration techniques, and the use of backdoor malware. This campaign poses severe risks to organizations, including data theft and operational disruption. Affected: Microsoft Management Console, businesses, organizations
Keypoints :
- Water Gamayun exploits CVE-2025-26633 to execute malicious code.
- The threat actor utilizes malicious provisioning packages and signed .msi files for payload deployment.
- Backdoors SilentPrism and DarkWisp are used for persistence and data theft.
- Payloads communicate with C&C servers over encrypted channels.
- Organizations can protect against these attacks through timely patch management and advanced threat detection.
- Trend Vision One™ has specific protections against the CVE-2025-26633 vulnerability.
MITRE Techniques :
- Tactic: Initial Access – Technique: Exploit Public-Facing Application (T1190) – Procedure: Water Gamayun exploits the CVE-2025-26633 vulnerability in Microsoft Management Console for initial access.
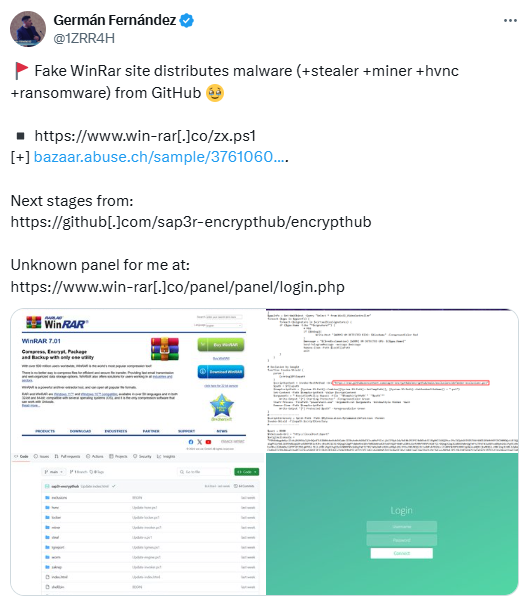
- Tactic: Execution – Technique: Command and Scripting Interpreter (T1059) – Procedure: Uses PowerShell scripts (e.g., worker.ps1, miner.ps1) to execute commands on compromised systems.
- Tactic: Persistence – Technique: Scheduled Task/Job (T1053) – Procedure: SilentPrism uses scheduled tasks based on user privileges to maintain persistence.
- Tactic: Exfiltration – Technique: Exfiltration Over Command and Control Channel (T1041) – Procedure: Data is exfiltrated through encrypted channels to the attacker’s C&C servers.
- Tactic: Credential Access – Technique: Credential Dumping (T1003) – Procedure: EncryptHub Stealer variants collect sensitive data like passwords and session data from various applications.
Indicator of Compromise :
- [MD5] abaa46bc704842d6cc6f494c21546ae6 (DingTalk_v7.6.38.122510801.msi)
- [MD5] f0df469c3459a6a3b98b7b69b07bf61b (worker.ps1)
- [SHA-256] cbb84155467087c4da2ec411463e4af379582bb742ce7009156756482868859c (DingTalk_v7.6.38.122510801.msi)
- [IP Address] 82[.]115[.]223[.]182 (malicious C&C server)
- [Domain] encrypthub.net, encrypthub.org (previously used C&C domains)
Full Story: https://www.trendmicro.com/en_us/research/25/c/deep-dive-into-water-gamayun.html