This report describes a worm-enabled npm supply-chain campaign that implanted install-time malware in multiple packages, harvested developer secrets and browser/wallet artifacts, exfiltrated data via an HTTPS webhook and an Internet Computer canister (cjn37-uyaaa-aaaac-qgnva-cai), and attempted self-propagation by republishing compromised packages and targeting PyPI. The activity shows strong tradecraft and code overlap with prior CanisterWorm incidents and is linked to TeamPCP–style supply chain attacks affecting packages tied to Namastex Labs’ Automagik ecosystem. #TeamPCP #NamastexLabs
Keypoints
- Multiple legitimate npm packages were modified to include install-time malware that executes during postinstall and targets developer environments for credential theft and propagation.
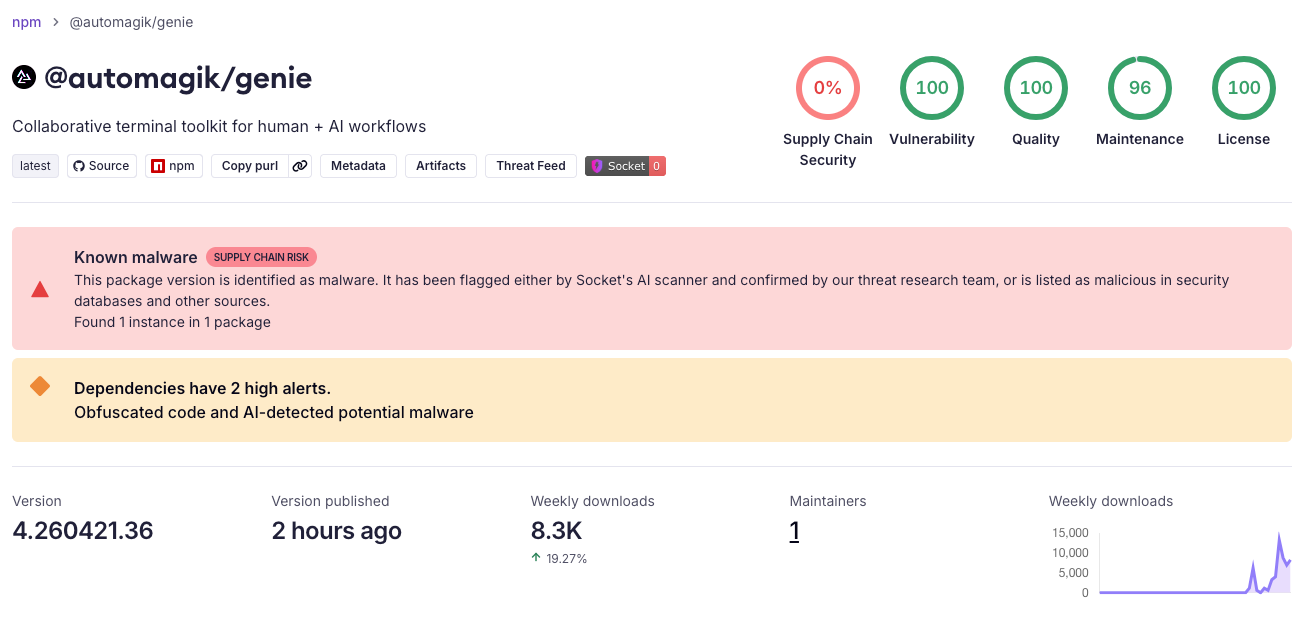
- Compromised packages include @automagik/genie (versions 4.260421.33–4.260421.39) and pgserve (1.1.11–1.1.13), plus sibling compromises observed in @fairwords and @openwebconcept packages, suggesting shared malware lineage or builder infrastructure.
- The malware harvests a broad set of secrets and high-value files (.npmrc, SSH keys, .git-credentials, netrc, cloud credentials, Kubernetes/Docker configs, Terraform/Pulumi/Vault material, .env files, shell history) and attempts to steal browser and crypto-wallet artifacts (Chrome login storage, MetaMask/Phantom extensions, Solana/Ethereum/Bitcoin/Exodus/Atomic wallet files).
- Exfiltration is performed to both a conventional HTTPS webhook (telemetry.api-monitor[.]com) and an Internet Computer Protocol (ICP) canister endpoint (cjn37-uyaaa-aaaac-qgnva-cai.raw.icp0[.]io), with optional hybrid AES-256-CBC + RSA-OAEP-SHA256 encryption using an embedded RSA public key.
- The implant includes worm-like propagation: extracting npm tokens, downloading and modifying package tarballs to inject a malicious postinstall hook and republishing, plus PyPI propagation via .pth-based payloads and Twine uploads when credentials are present.
- Defensive guidance: treat affected versions as malicious, block/remove identified package versions, rotate npm/GitHub/cloud/SSH credentials, audit publish histories and internal mirrors for IOCs, and compare npm tarballs to public GitHub tags to detect release anomalies.
MITRE Techniques
- [T1059 ] Command and Scripting Interpreter – postinstall JavaScript is executed at install time to run the malicious payload (‘install-time execution through postinstall’).
- [T1546 ] Event Triggered Execution – Python .pth injection is used for persistence and PyPI propagation (‘Technique: .pth file injection (TeamPCP/LiteLLM method)’).
- [T1005 ] Data from Local System – the script reads numerous high-value files and environment data from the victim system for collection (‘It also reads high-value files from the local system, including: .npmrc SSH keys and SSH config .git-credentials .netrc … shell history files’).
- [T1552.001 ] Credentials in Files – harvested credentials and tokens are taken from local configuration files and environment variables (‘The script collects sensitive environment variables by matching names commonly associated with secrets, tokens, credentials…’).
- [T1555 ] Credentials from Password Stores – the payload targets browser-stored credentials and wallet extension data to steal secrets (‘access browser and crypto-wallet artifacts, including Chrome login storage and extension data associated with MetaMask and Phantom’).
- [T1567 ] Exfiltration Over Web Service – stolen data is sent to a hosted webhook service and an ICP canister endpoint for off-host exfiltration (‘The malware exfiltrates stolen data to both a conventional webhook and an ICP canister endpoint’).
- [T1071 ] Application Layer Protocol – the malware uses HTTPS and HTTP requests to communicate with C2/exfiltration endpoints (example: ‘const req = https.request… hostname: `${ICP_CANISTER_ID}.raw.icp0.io`’).
- [T1195 ] Supply Chain Compromise – the attacker abuses publisher credentials and package publish flows to inject malicious postinstall hooks and republish compromised packages across npm and PyPI (‘extract npm tokens … inject a new malicious postinstall hook … and republish the packages’).
Indicators of Compromise
- [File Hash ] malicious distributed files – dist/env-compat.cjs: c19c4574d09e60636425f9555d3b63e8cb5c9d63ceb1c982c35e5a310c97a839, dist/public.pem: 834b6e5db5710b9308d0598978a0148a9dc832361f1fa0b7ad4343dcceba2812
- [Domain / Endpoint ] exfiltration webhook hosts – telemetry.api-monitor[.]com/v1/telemetry, telemetry.api-monitor[.]com/v1/drop (used as HTTPS webhook exfil endpoints)
- [Canister ID ] ICP canister C2 – cjn37-uyaaa-aaaac-qgnva-cai (hardcoded canister used as a dead-drop command-and-control channel)
- [Package Names / Versions ] compromised npm packages and versions – @automagik/[email protected]–4.260421.39 (e.g., @automagik/[email protected]), [email protected]–1.1.13 (e.g., [email protected]), plus @fairwords and @openwebconcept impacted releases
- [RSA Public Key Fingerprint ] embedded public key – DER SHA-256: 87259b0d1d017ad8b8daa7c177c2d9f0940e457f8dd1ab3abab3681e433ca88e (used to encrypt stolen data when present)
- [Distinctive Strings ] unique markers and telemetry strings – ‘node dist/env-compat.cjs || true’, ‘pkg-telemetry’, ‘dist-propagation-report’ (useful for hunting sibling builds)
- [File Names ] targeted configuration and secret files – .npmrc, .git-credentials, netrc, .env* (files enumerated by the malware for credential harvesting)
- [HTTP Headers ] custom request headers seen in exfiltration – X-Session-ID, X-Request-Signature (used when sending data to the webhook)
Read more: https://socket.dev/blog/namastex-npm-packages-compromised-canisterworm