Microsoft observed the North Korea-aligned threat actor Jasper Sleet using stolen or fabricated identities and generative AI to pose as legitimate remote IT hires, abusing Workday and external career-site APIs to infiltrate organizations. The actor leverages external infrastructure and legitimate onboarding workflows to gain valid accounts, set up payroll, and access internal SaaS like Teams, SharePoint, OneDrive, and Exchange Online. #JasperSleet #Workday
Keypoints
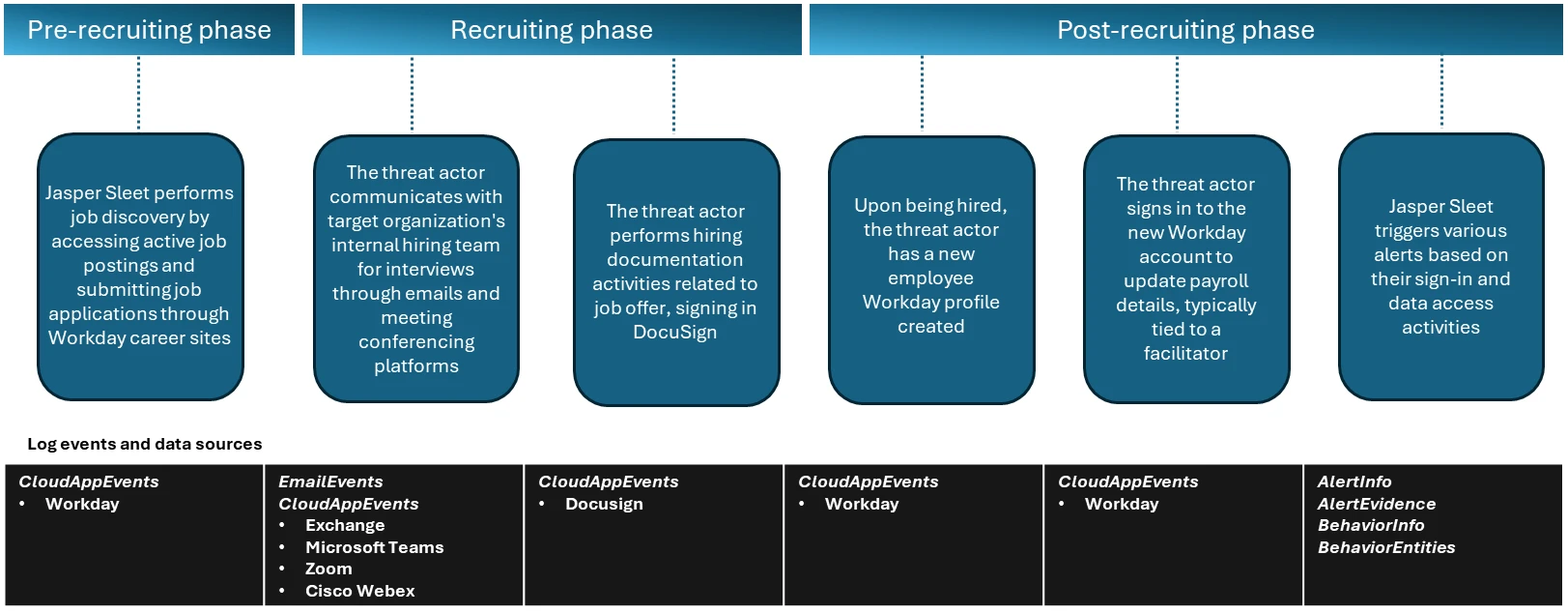
- Jasper Sleet uses generative AI to analyze job postings and build tailored fake personas that increase the chance of passing recruitment screenings and onboarding.
- The actor targets external-facing HR SaaS APIs (Workday Recruiting Web Service) and career sites to discover open technical roles and interact programmatically with recruitment endpoints.
- Microsoft observed API calls to hrrecruiting endpoints (e.g., hrrecruiting/accounts/*, hrrecruiting/jobApplicationPackages/*, hrrecruiting/validateJobApplication/*, hrrecruiting/resumes/*) originating from known actor infrastructure.
- During recruiting, threat actors communicate via email, Microsoft Teams, Zoom, Cisco Webex, and use DocuSign for hiring documentation to appear legitimate.
- After hire, actors sign in with legitimate accounts, update payroll details, and access internal SaaS (Teams, SharePoint, OneDrive, Exchange Online), generating anomalous alerts like impossible travel.
- Microsoft recommends enabling Defender for Cloud Apps connectors, correlating Workday telemetry with threat intelligence, and monitoring behavioral anomalies across recruitment and onboarding.
MITRE Techniques
- [T1583 ] Acquire Infrastructure – The actor used known external infrastructure to access Workday Recruiting Web Service endpoints exposed via external career sites (‘accessing Workday Recruiting Web Service endpoints exposed through external career sites from known actor infrastructure and email accounts’)
- [T1589 ] Gather Victim Identity Information – The actor used generative AI to analyze job postings and extract role‑specific language, skills, and tooling expectations to craft convincing fake personas (‘use generative AI at scale to analyze job postings and extract role‑specific language, required skills, certifications, and tooling expectations’)
- [T1078 ] Valid Accounts – After successful hiring and onboarding, the threat actor used the legitimately created Workday account to sign in and access internal resources (‘a legitimate account is created and assigned to them as part of the onboarding process’)
- [T1098 ] Account Manipulation – The actor performed payroll and finance-related changes during onboarding to set up payment details and persistence (‘sign-ins to the newly created Workday profile and setting up of payroll details originating from known Jasper Sleet infrastructure’)
Indicators of Compromise
- [IP Address ] External infrastructure and suspicious access to recruitment and communication tools – “suspiciousIPs” (placeholder for observed malicious IPs), “known Jasper Sleet infrastructure IPs”
- [Email / Account IDs ] External accounts used in recruitment and communications – “suspicious_emailids” (placeholder for observed malicious email/account identifiers), “NewHireWorkdayId” (example Workday account identifier used in queries)
- [API Endpoints ] Programmatic access to recruitment services in Workday – hrrecruiting/accounts/*, hrrecruiting/jobApplicationPackages/* (used to enumerate jobs and submit applications)
- [Application / Service Names ] Targeted SaaS and collaboration services used in the campaign – Workday, Microsoft Teams, Zoom, Cisco Webex, DocuSign, SharePoint, OneDrive, Exchange Online