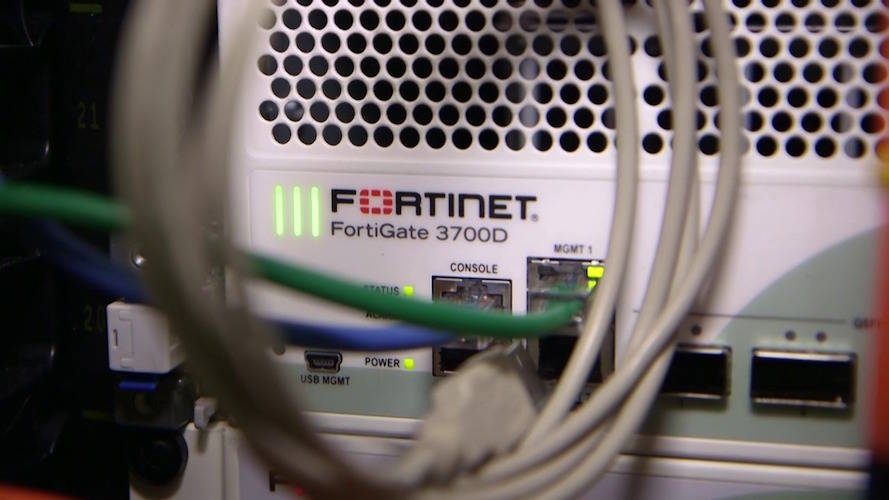
The volume of Fortinet boxes exposed to the public internet and vulnerable to a month-old critical security flaw in FortiOS is still extremely high, despite a gradual increase in patching.
According to security nonprofit Shadowserver’s latest data, the number of Fortinet appliances vulnerable to CVE-2024-21762 stands at more than 133,000 – down only slightly from more than 150,000 ten days prior.
Fortinet patched CVE-2024-21762 in early February, well over a month ago. It’s a 9.6-out-of-10 severity vulnerability that leads to remote code execution (RCE) and appeared front and center during Fortinet’s week to forget last month.
The biggest number of exposures is in Asia, with 54,310 appliances still vulnerable to the critical RCE bug, the data shows. North America and Europe fill the second and third spots with 34,945 and 28,058 respectively, while South America, Africa, and Oceania comprise the remainder.
The number of exposed SSL VPNs illustrates the wide attack surface for the critical vulnerability, one that’s already known to be actively exploited.
When it was first disclosed by Fortinet, the vendor said there was evidence of it being used as a zero day. The US government’s Cybersecurity and Infrastructure Security Agency (CISA) soon corroborated this by adding it to the Known Exploited Vulnerability (KEV) catalog, thereby requiring all federal agencies to patch it within a tight deadline.
Proof of concepts are now relatively widely available online, meaning the likelihood of an attacker scanning for vulnerable boxes and popping one open is as high as it has been since the vulnerability was disclosed. Swift patching is very strongly recommended.
“This was another case of a network/security appliance having a pretty serious memory corruption vulnerability,” said Dylan Pindur, security researcher at Assetnote. “It’s also far from the first for FortiGate. As is often the case with these issues the mitigations are known, it’s just whether or not they are applied.”
Woes continue
As Pindur notes, CVE-2024-21762 was just one vulnerability that’s been giving admins headaches recently. To make matters worse, the vendor announced another critical-severity bug that led to RCE last week, further adding to the patching workload.
CVE-2023-48788 is an SQL Injection flaw in FortiClient Endpoint Management Server (EMS) that was disclosed on March 12, carrying a 9.3 severity score.
Although there’s no mention of it being actively exploited, experts at Tenable said it was likely to happen soon.
Researchers at GreyNoise have begun tracking active exploits of CVE-2023-48788, but at the time of writing the data shows no signs of malicious activity.
“Due to prior targeting of Fortinet devices and word of an upcoming proof of concept exploit for the flaw, in-the-wild exploitation is likely to occur,” said Chris Boyd, staff research engineer at Tenable.
“Fortinet’s FortiOS and FortiProxy have been popular targets for threat actors, including CVE-2023-27997, a critical heap-based buffer overflow, and CVE-2022-40684, a critical authentication bypass vulnerability.
“Other vulnerabilities in Fortinet devices have attracted the attention of multiple nation-state threat actors and ransomware groups like Conti. Fortinet vulnerabilities have been included as part of the top routinely exploited vulnerability lists in recent years.”
CISA also released an advisory a day before Fortinet’s disclosure of CVE-2024-21762, warning of Volt Typhoon pre-positioning itself inside US critical infrastructure, using vulnerabilities in networking appliances like Fortinet as a way in. For the uninitiated, Volt Typhoon is the name used to track a known state-sponsored offensive cyber group aligned with China. ®
Source: https://www.theregister.com/2024/03/18/more_than_133000_fortinet_appliances/?&web_view=true
“An interesting youtube video that may be related to the article above”